Nengine.dll Issues
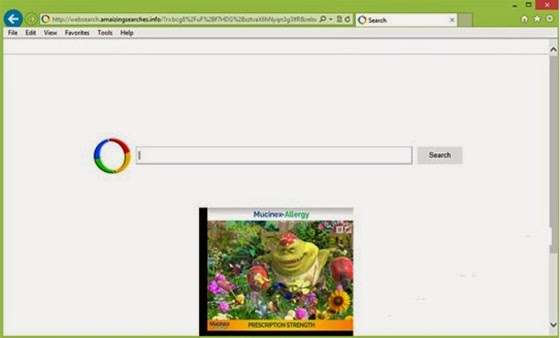
- Appdata\roaming\newnext.me\nengine.dll the specified module could not be found
- Nengine.dll is not a proper application extension
- Problem loading nengine.dll." C:\Users\User\AppData\Roaming\newnext.me\nengine.dll (PUP.Optional.NextLive.A)
What Is Nengine.dll
As its name suggests, nengine.dll is a dynamic link library file offering a solution for a process to call the function that doesn’t belong to its executable code. It should be informed that many applications are not a complete executable file; usually an application is divided into several comparatively independent .dll file when being installed onto a machine. According to the directory reported by Windows, nengine.dll is not a system file and must be the component of certain third-party program.