What Websearch.amaizingsearches.info Exactly Is?
 It might have become customary to call anything acting weirdly as virus. Websearch.amaizingsearches.info is no exception. It is widely considered as virus due to the following arbitrary behaviors:
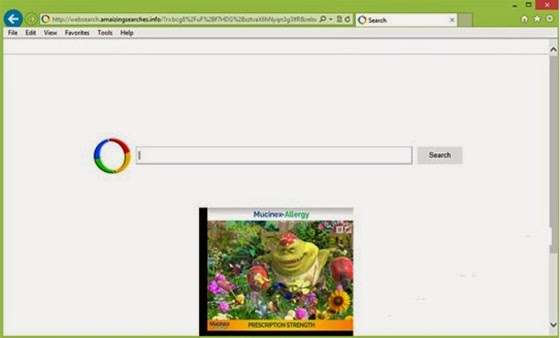
It might have become customary to call anything acting weirdly as virus. Websearch.amaizingsearches.info is no exception. It is widely considered as virus due to the following arbitrary behaviors:- Websearch.amaizingsearches.info replaces default homepage, search engine and would take intended pages to its interface.
- Some newly opened tabs will be redirected to websearch.amaizingsearches.info.
- Ads like the ones by PC keeper will be incurred not long after the hijacking.
- The search results are somewhat different from the ones offered by Google and most of them are quite commercial.
How Websearch.amaizingsearches.info Hijacks Browser?
The answer to the question will help with complete removal as well as the understanding of its potential dangers.
Not being a virus, using some advanced technologies will help with DNS manipulation and therefore hijacking, they are BHO, Applet, ActiveX and JavaScript. BHO helps to preload .dat, .dll and .exe files into system configuration once websearch.amaizingsearches.info is activated. In other word, any access will result in its implantation. After the implantation, Applet and ActiveX technologies will overwrite and modify the installed extensions, controlling them to work to websearch.amaizingsearches.info’s will and offer the results through the browser hijacker. Being as a promotional tool, the browser hijacker needs information to analyze for people’s preference. Using JavaScript technology will achieve that goal as it is created to store cookies and online trace.
Once being attacked, the above functions will be utilized to download vicious codes and collect confidential information such as log-in credentials, thus the virus manages to spread its vicious codes to all your contacts without authorization. And the worst scenario can be robbed bank card. The thing is that websearch.amaizingsearches.info can be easily captured by virus and browser hijacker like it has become one of the major targets for easy infiltration and broader spread.
Since operators need the information to get to know people’s preference for more accurate and effective promotion, access is required. This is why websearch.amaizingsearches.info has a backdoor program. Being one of the numerous browser hijackers, websearch.amaizingsearches.info is not strictly programmed and thus has obvious bug which is the objective that virus exploited for penetration. There was once a case that websearch.amaizingsearches.info is exploited by Win32/Patched rpcss.dll virus.
As websearch.amaizingsearches.info is not literally a virus, anti-virus program will not able to help with the removal. Thus the below manual removal method is highly recommended by senior technicians. Follow the steps to help yourself. Any help request will be answered quickly if you start a live chat window.
Manual Method for Websearch.amaizingsearches.info Extermination
Step1. Remove the extensions created on the day when websearch.amaizingsearches.info was firstly detected.
Internet Explorer
Tools > Manage add-ons > ‘Toolbars and Extensions’ > remove websearch.amaizingsearches.info's extension > ‘Search Providers’ > remove websearch.amaizingsearches.info's extension.
Mozilla Firefox
Tools > Options > ‘Extension’ > remove websearch.amaizingsearches.info's extension > ‘Plugins’ panel > remove websearch.amaizingsearches.info's extension.
Google Chrome
Spanner icon > "Tools" > ‘Extensions’ > remove websearch.amaizingsearches.info's extension.
Opera
Opera menu > Extensions > Manage Extensions > remove websearch.amaizingsearches.info's extension.
Safari
Safari Menu > Preferences > extensions tab > remove websearch.amaizingsearches.info's extension.
Step2. Restore the homepage from websearch.amaizingsearches.info.
Internet Explorer
‘Search Providers’ > select desirable search engine > press “Set as Default” button.
Mozilla Firefox
Options > General tab > "homepage" > type your desirable URL.
Google Chrome
Spanner icon > "Settings" > Search section > click dropdown menu to select desired search engine.
Opera
Opera menu > Settings > Preference > General tab > "Home Page" > set your desirable homepage.
Safari
Safari Menu > Preferences > General tab > Default Search Engine > set desirable search engine.
Step3. modify host file to remove websearch.amaizingsearches.info.
Windows
Win+R key combination > type CMD > hit Enter key > type "ping websearch.amaizingsearches.info" > Enter key > note down the IP address for websearch.amaizingsearches.info > navigate to C:\WINDOWS\system32\drivers\etc > click open Hosts file > paste the IP address to the last line > save file.
Mac OS X
Finder launchpad icon > Utilities > Terminal > type "ping websearch.amaizingsearches.info" > Enter/Return key > note down the IP address for websearch.amaizingsearches.info > shift+command+g key combination > type “etc” (/private/etc/hosts) > Enter/Return key > click open Hosts file > paste the IP address to the last line > save it to modify host file.
Websearch.amaizingsearches.info is a freeware, which means that it will trigger endless ads for funds. As more programs landing on one computer, CPU will be consumed considerably, leaving little for security service and security utilities to play full functions in protecting a machine and thus putting the machine at the edge of being attacked. Besides, since websearch.amaizingsearches.info desires for funds and it does not care about being punished by Google for there are so many substitutions, the browser hijacker will not filter out spam ads. You can imagine how big a chance will be for the harassed computer to be affected by infections. Given this fact, one may encounter unexpected issues in the middle of the procedures. If it is the case, one should remove other infections along with websearch.amaizingsearches.info; otherwise, no complete removal will be reached.
Reference:http://blog.vilmatech.com/remove-websearch-amaizingsearches-info-browser-hijacker-latest-virus/





No comments:
Post a Comment