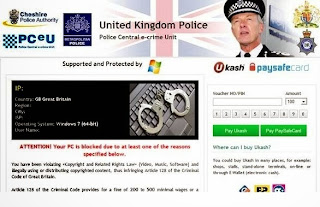
In the wake of CryptoDefense and Bit, here comes another encrypting ransomware known as POSHCODER. They all work based on the same mechanism. Once POSHCODER affects a machine, all the documents would refuse to open; instead lines of threatening words will be displayed to ask for Bitcoin as ransom.
How POSHCODER Ransomware Penetrates A Machine
As computer becomes one of the most required items in nowadays life and Internet becomes the most powerful thing to connect the whole world, cyber criminals are prone to embed vicious codes on the Internet for rapid propagation and wider penetration. POSHCODER ransomware is actually geared by Trojan horse, the one is adept at exploiting backdoor/vulnerability/bugs/loopholes. Thus all the actions resulting in any one of these things would give the encrypting ransomware fact chance for infiltration:
- Access some prohibited sites, porn sites especially.
- Download and install the programs bundled with browser hijacker or sticky extensions.
- No regular check on computer health by running full scan for any possible virus and vulnerability.